Table Showing Cyber Attack Methods And Technology For Internet Security | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

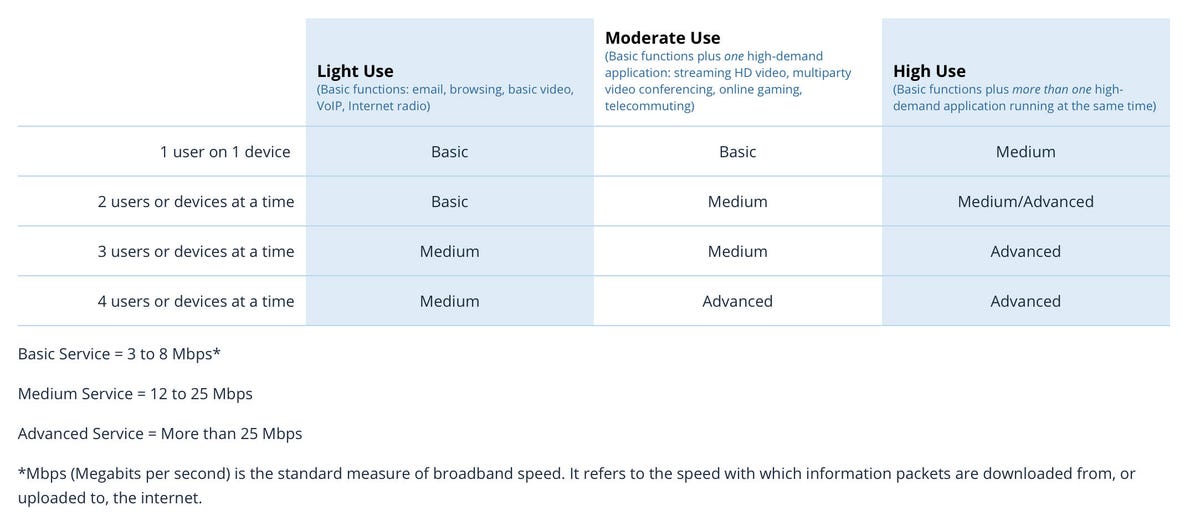
Internet Plans Pricing Table Along With Features | PowerPoint Slide Template | Presentation Templates PPT Layout | Presentation Deck
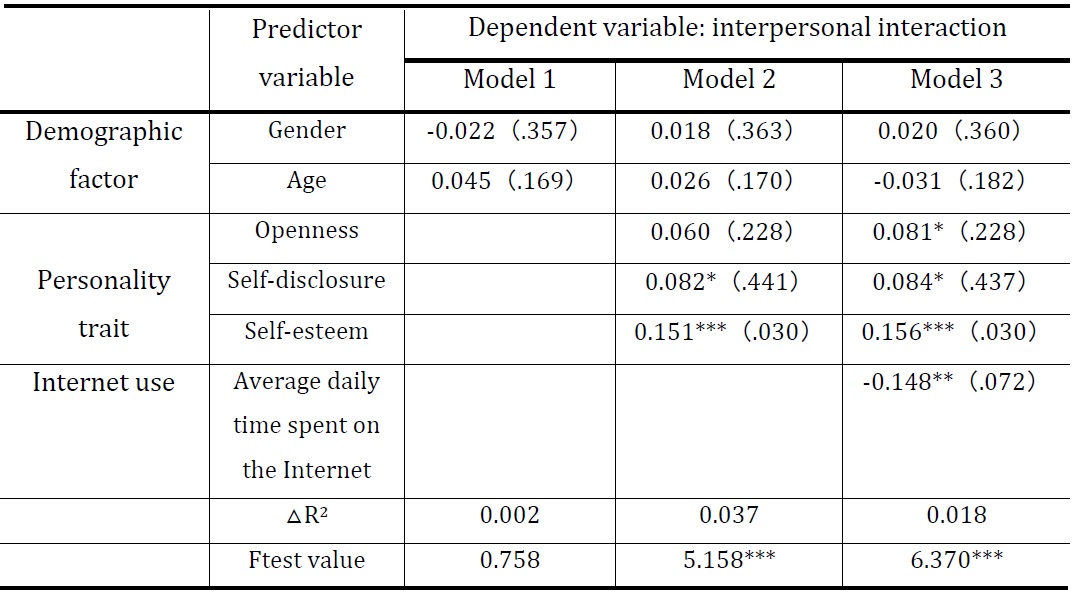
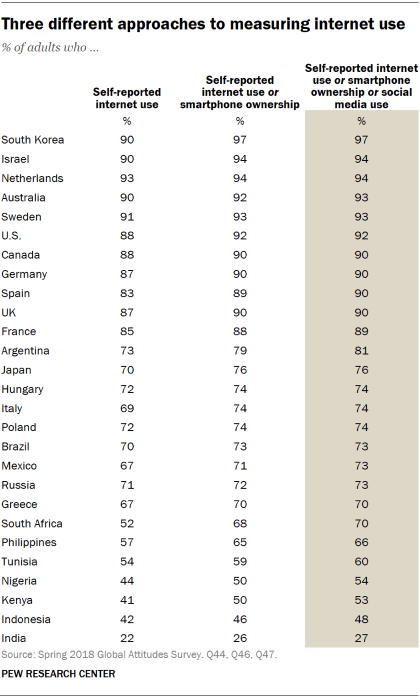
The Influence of Internet Use on Interpersonal Interaction Among Chinese Urban Residents: The Mediating Effect of Social Identification | Published in Asian Journal for Public Opinion Research

Table 1 from Internet of Things (IoT): Application systems and security vulnerabilities | Semantic Scholar

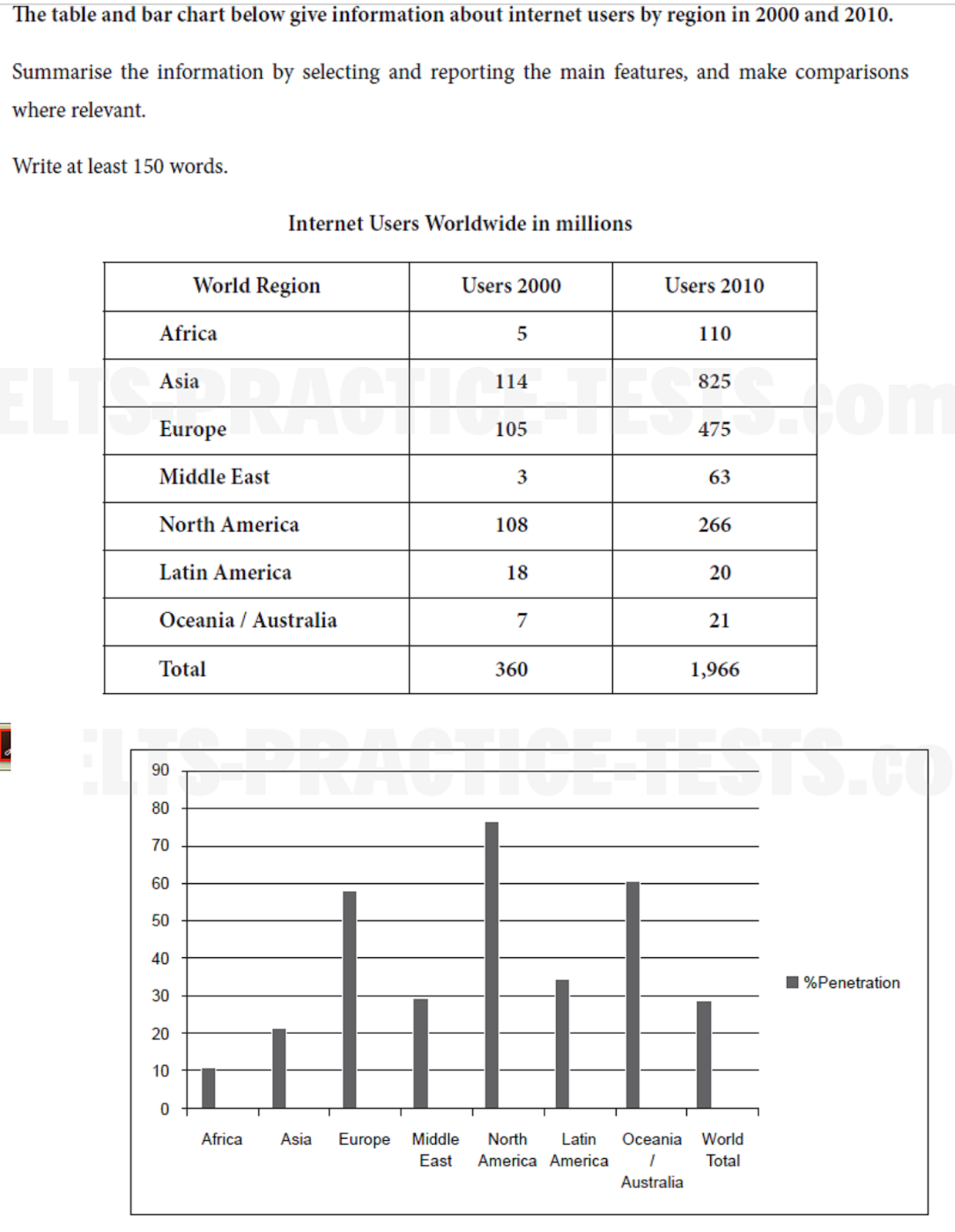
IQ Bamboo Language Services - IELTS Prep - Academic Task 1 - Internet Activities by Age Group Table Sample Task The table below gives information on internet use in six categories by

Internet Plans Pricing Table Along With Features | PowerPoint Slide Template | Presentation Templates PPT Layout | Presentation Deck










![PDF] The Evolution of Internet Services | Semantic Scholar PDF] The Evolution of Internet Services | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c2a530ed77da6ae750c00bc0467241f66e359bda/8-Table1-1.png)